LDAP Configuration
LDAP Configuration Overview
If your organization already manages users in LDAP or Active Directory, you can connect IOMETE to that directory to import users and groups and let LDAP users sign in with their existing credentials.
Open Settings → IAM → LDAP to configure the integration. Only users with the IAM Manager admin role can access this page.
Each IOMETE installation supports a single, platform-wide LDAP configuration. The configuration is shared across all workspaces and clusters in the installation.
Configuration
General Options
The General Options section includes the following settings:
- Connection URL: The URL to connect to your LDAP server. Example:
ldap://openldap.infra.svc:389 - Bind DN: The distinguished name (DN) used for binding to the LDAP server. This bind DN must have the necessary permissions on the LDAP directory. Example:
cn=admin,dc=iomete,dc=com - Bind credential: The password for the bind DN.
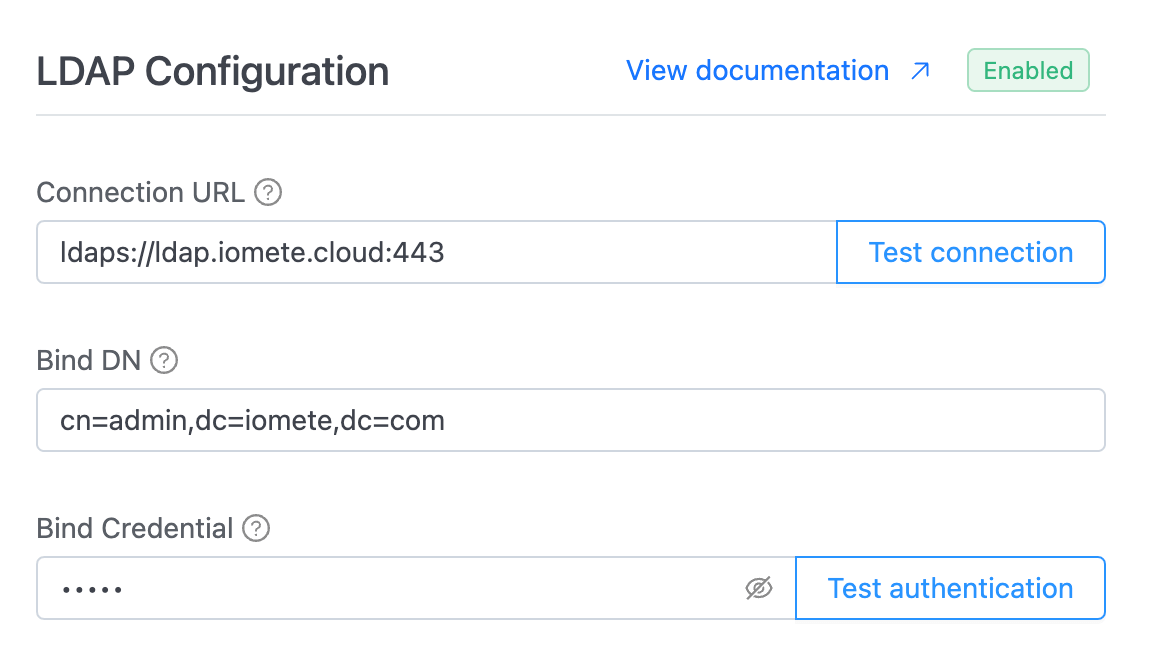
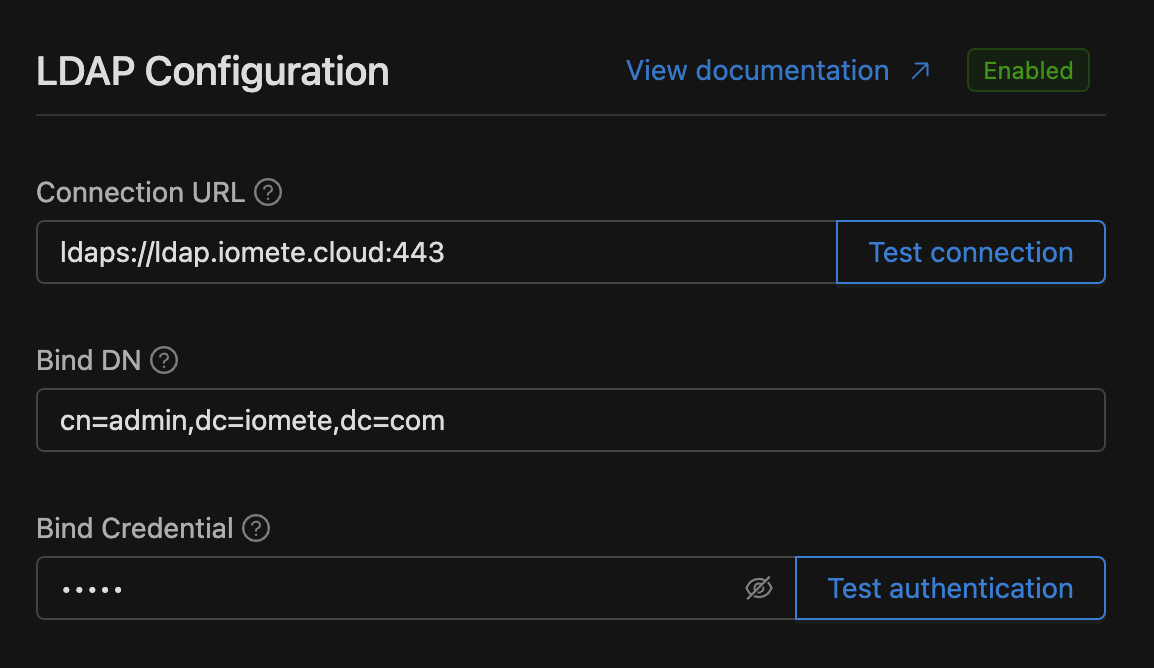
Use Test connection after entering the Connection URL to verify that IOMETE can reach the LDAP server.
Use Test authentication after entering the Connection URL, Bind DN, and Bind credential to verify that the bind credentials work.
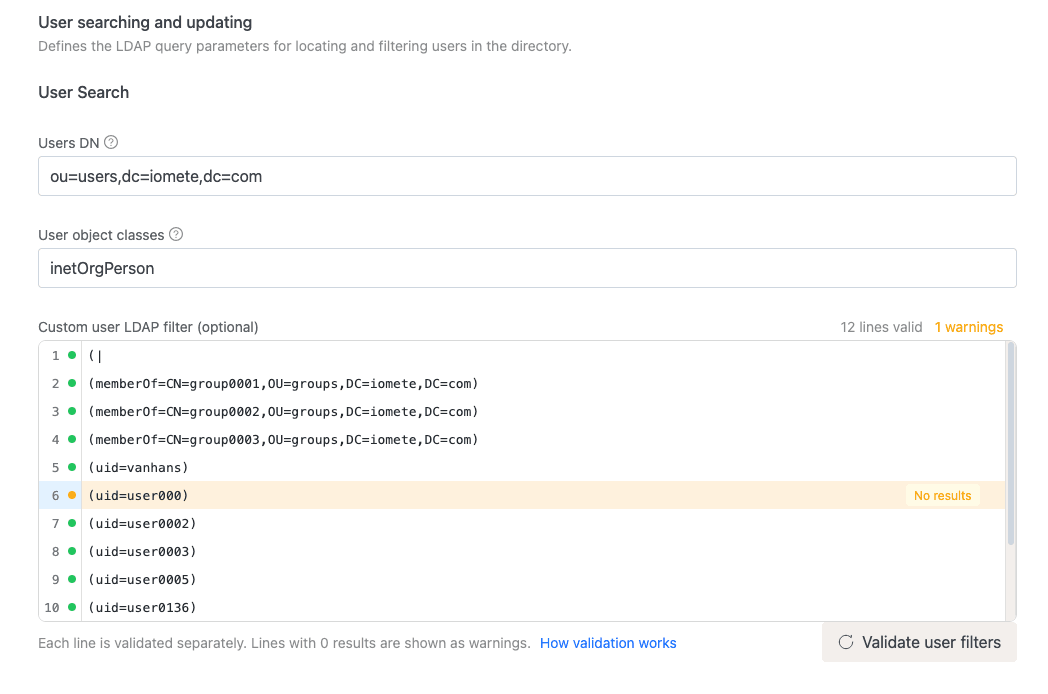
User Searching and Updating
Defines the LDAP query parameters for locating and filtering users in the directory.
User Search
- Users DN: The full DN where the users are located in the LDAP directory. This DN is the parent of LDAP users. Example:
ou=users,dc=iomete,dc=com. - User object classes: A comma-separated list of object classes that identify LDAP user objects. Example:
inetOrgPerson, organizationalPerson. - Custom user LDAP filter (Optional): Add a custom filter to refine user search. Enter one LDAP filter per line in the editor.
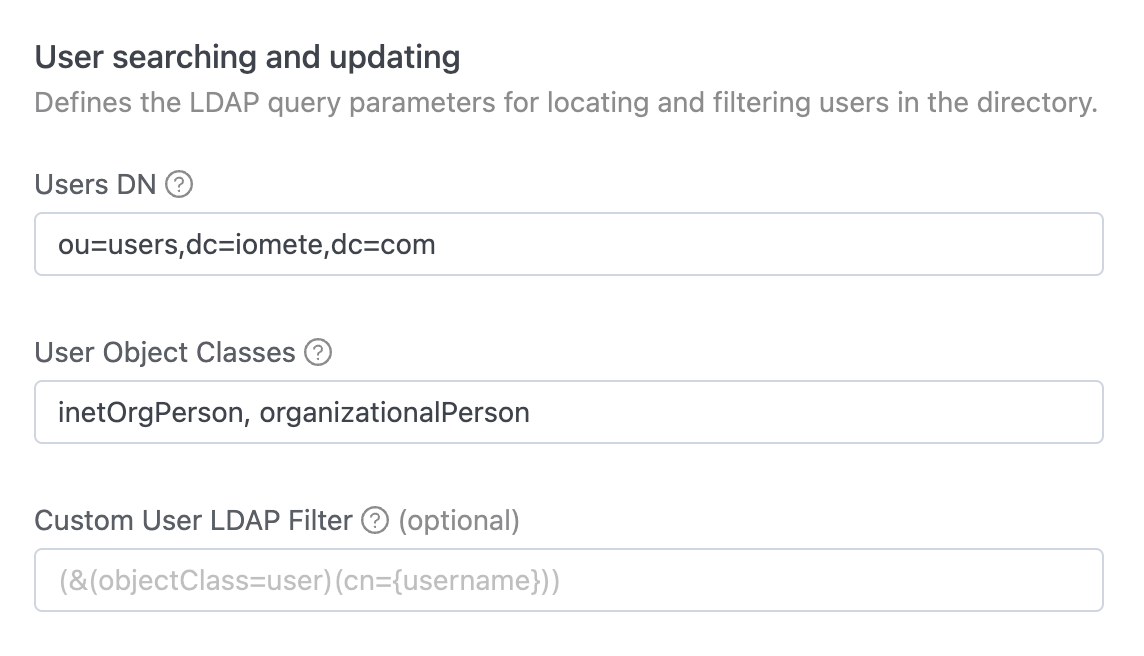
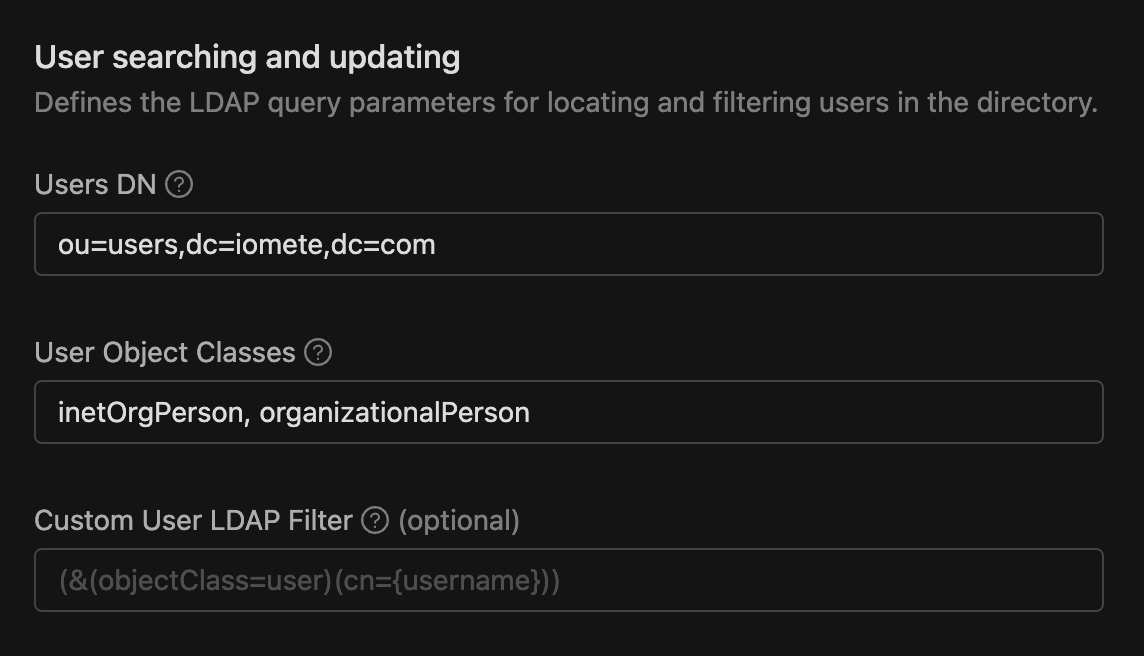
Use Validate user filters to check each non-empty filter line before saving. See Validating LDAP Filters for details.
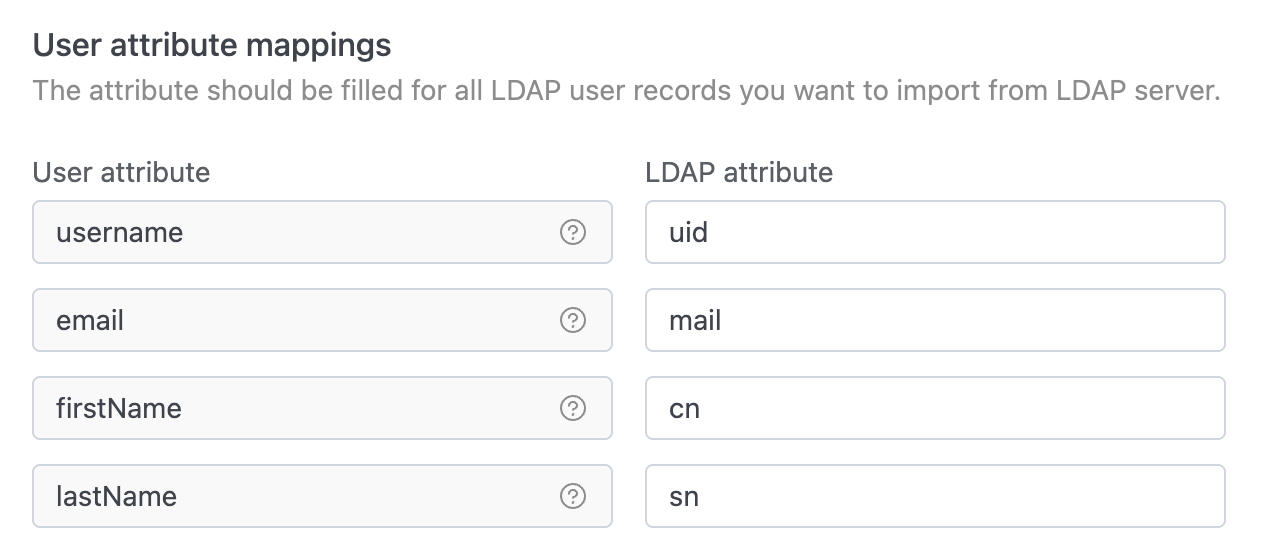
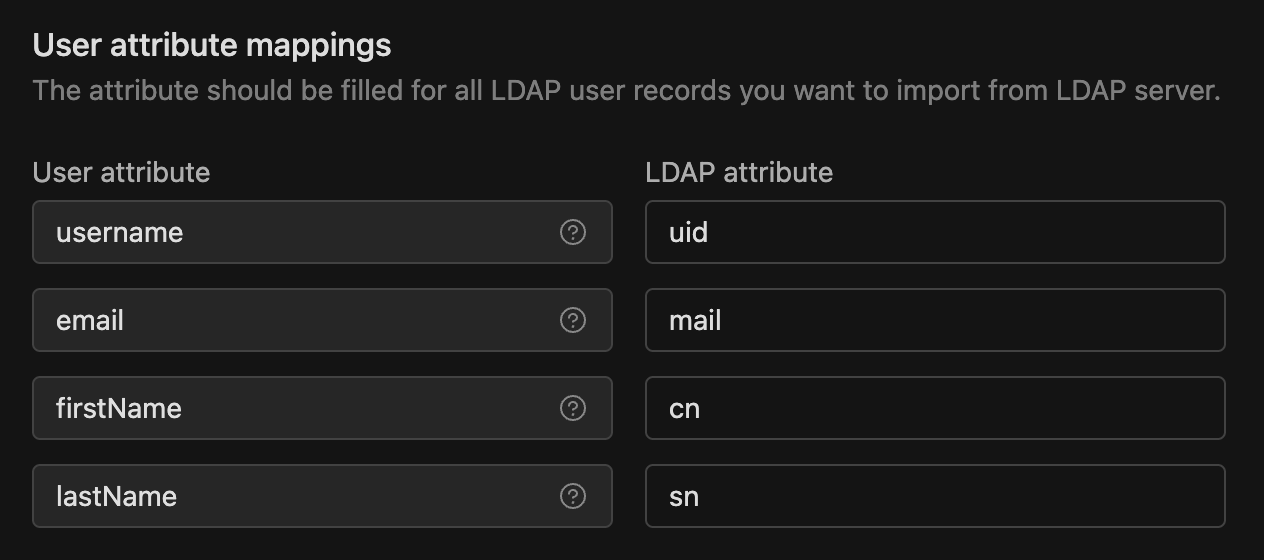
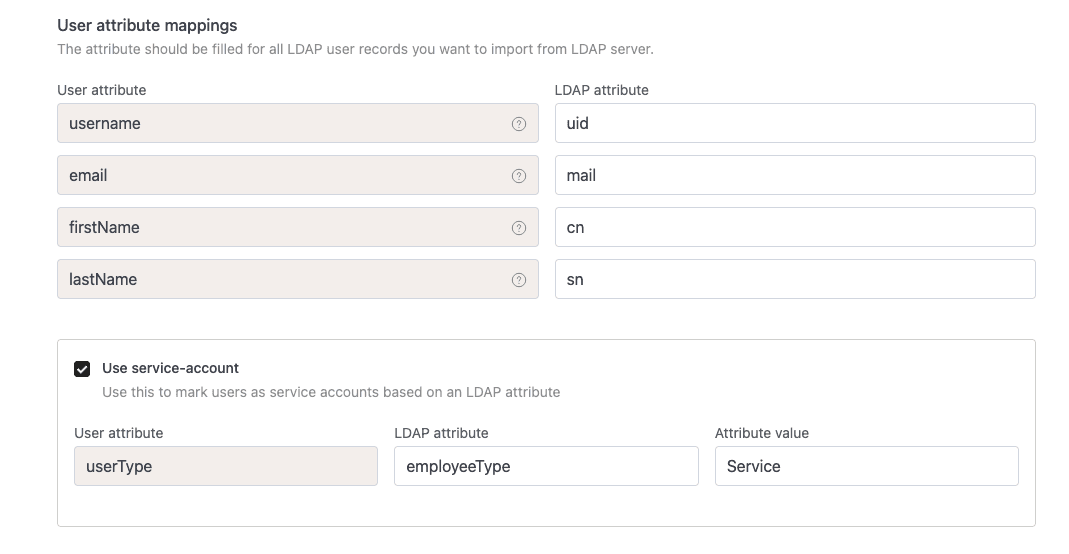
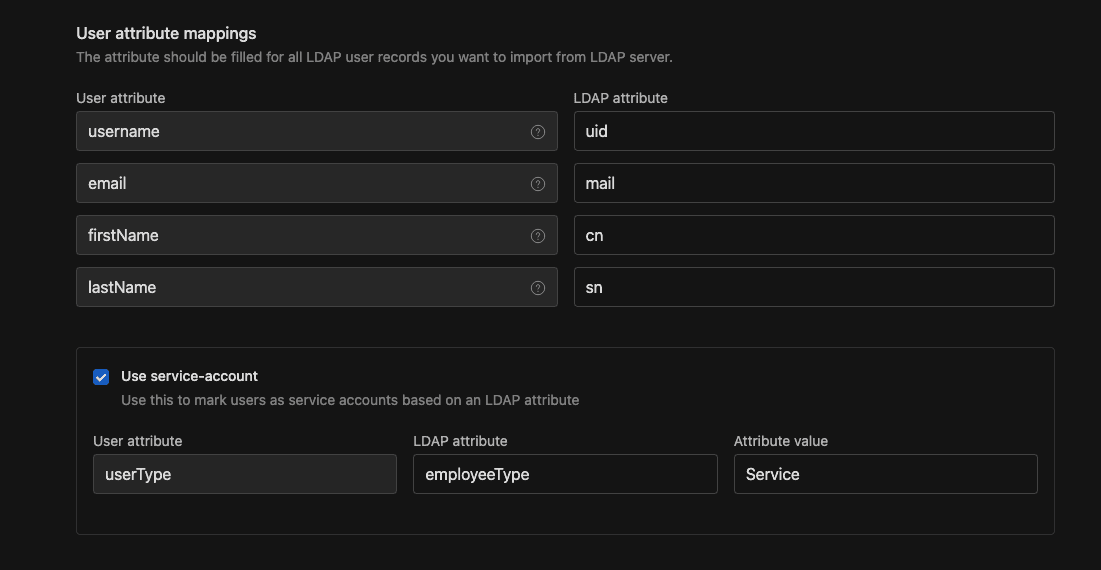
User Attribute Mappings
Map each IOMETE user attribute to the corresponding LDAP attribute so that user information is correctly retrieved from the directory.
- username: LDAP attribute mapped as the IOMETE username. Commonly
uidfor many LDAP servers, andsAMAccountNameorcnfor Active Directory. - email: LDAP attribute mapped as the IOMETE email. Typically
mailfor most LDAP servers. - firstName: LDAP attribute mapped as the IOMETE first name. Default
cn(common name). - lastName: LDAP attribute mapped as the IOMETE last name. Commonly
sn(surname).
To mark some imported users as service accounts based on an LDAP attribute, enable Use service-account. Three columns appear:
- User attribute: Always
userType(read-only). This is the IOMETE-side identifier. - LDAP attribute: The LDAP attribute that IOMETE inspects on each user. Example:
employeeType. - Attribute value: The value that marks the user as a service account. Example:
Service.
Imported users whose LDAP attribute equals this value are created as service accounts instead of person accounts. You can manage their API access with service account access tokens.
Group Search
Defines how LDAP groups are searched and mapped, including the DN base, object classes, filter, and group attribute mappings. This section is optional.
Select Group searching and updating to enable group sync. When the checkbox is unchecked, the rest of the group fields are hidden and IOMETE only syncs users.
- Groups DN: Defines the LDAP tree where groups are located. Example:
ou=groups,dc=iomete,dc=com. - Group object classes: A comma-separated list of object classes that identify LDAP group objects. Example:
groupOfNames. - Custom group LDAP filter (Optional): Add a custom filter to refine group searches. Enter one LDAP filter per line in the editor.
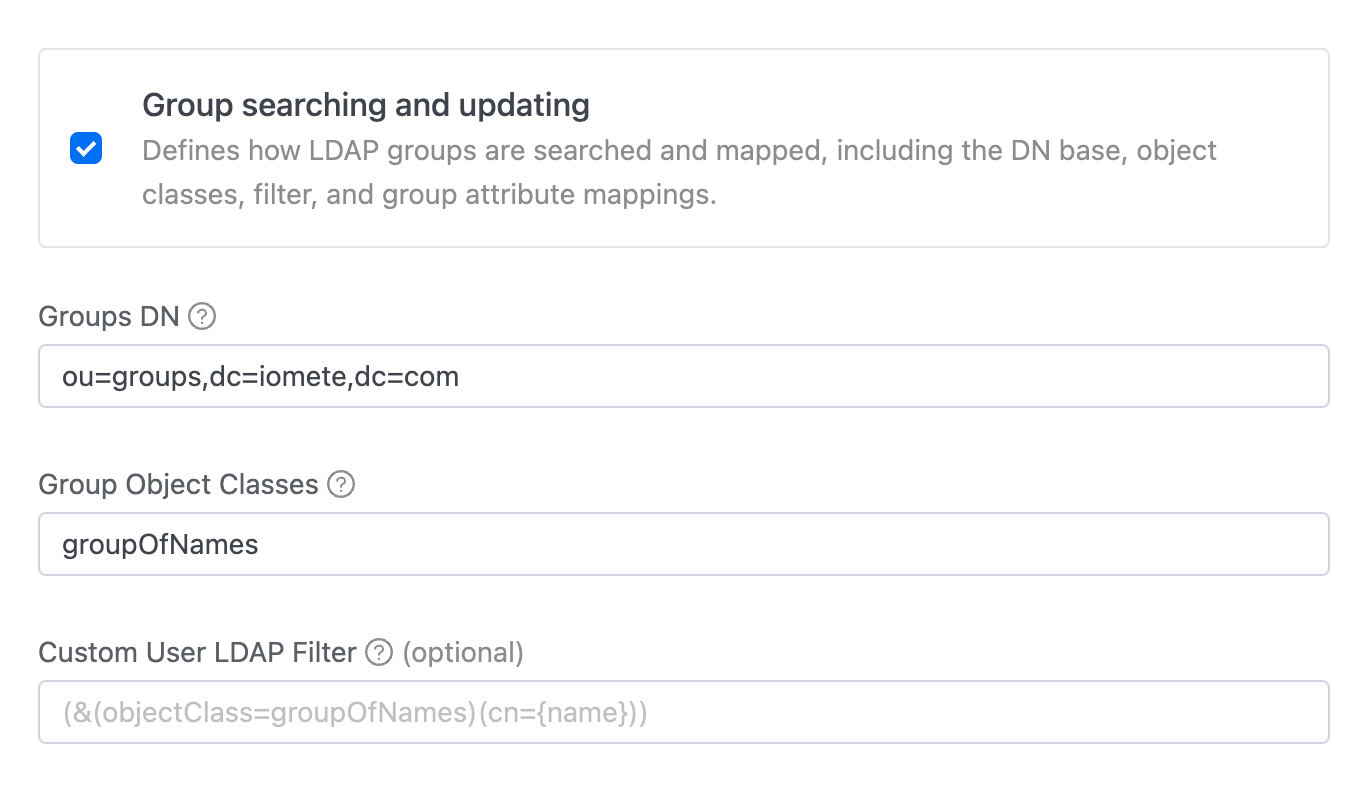
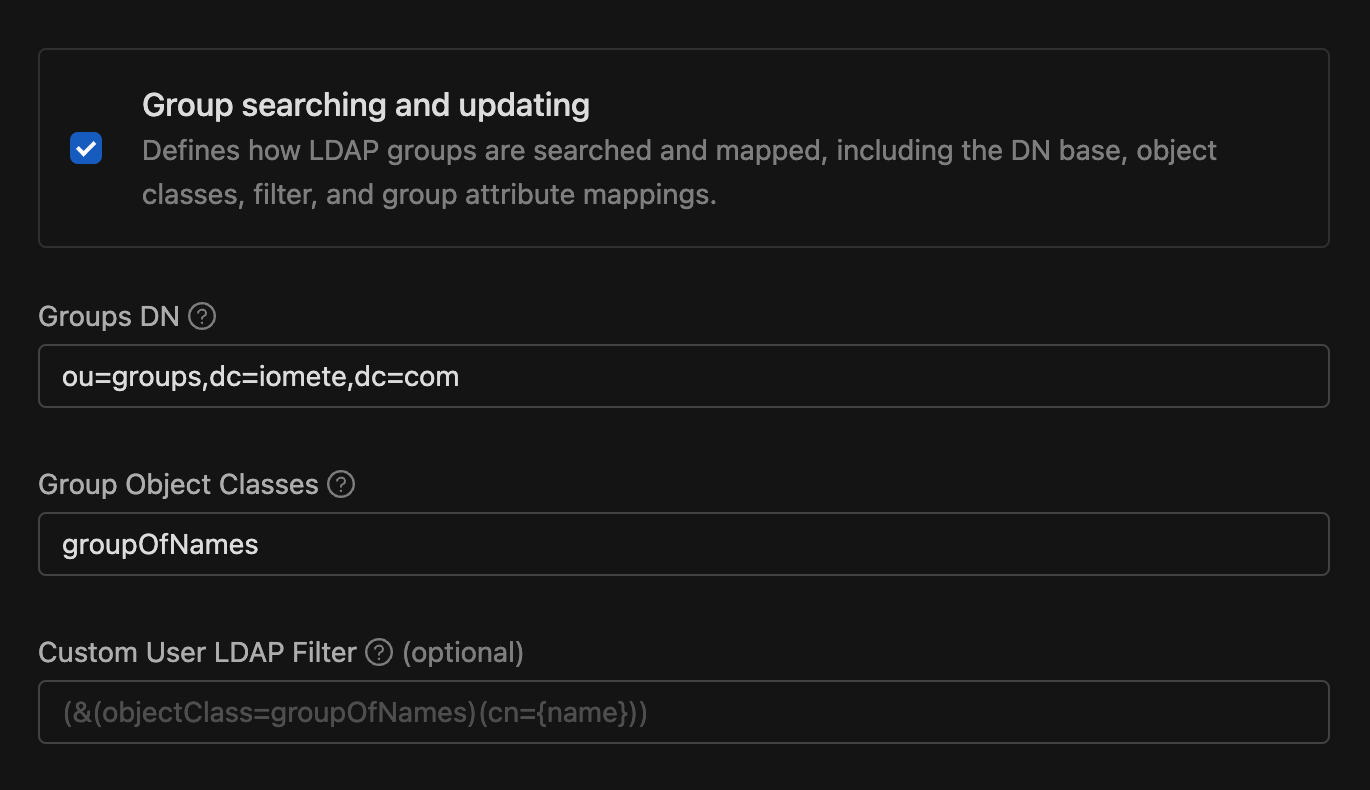
Use Validate group filters to check group filter lines before saving.
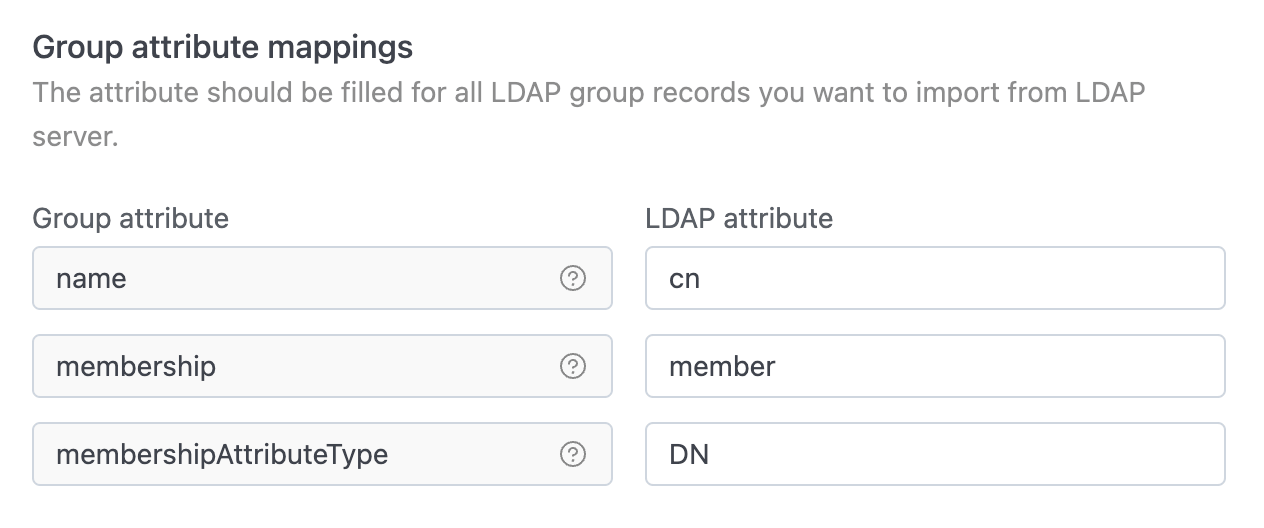
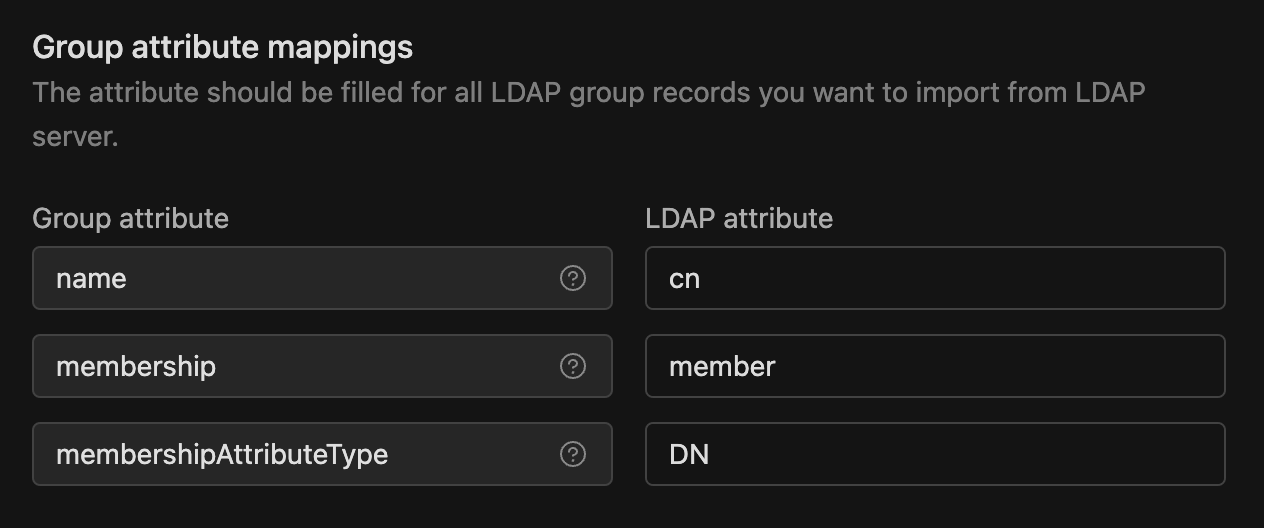
Group Attribute Mappings
Fill these attributes for the LDAP group records you want to import from the directory.
- name: The LDAP attribute used for group names and RDN is typically
cn. For example, a group's DN might look likecn=Group1,ou=groups,dc=example,dc=org. - membership: The LDAP attribute used for group membership mapping is typically
member. - membershipAttributeType: Specifies the type of the membership attribute. Choose
DNorUID.DNrepresents the full path to the user in the directory, whileUIDrefers to the user's unique identifier.
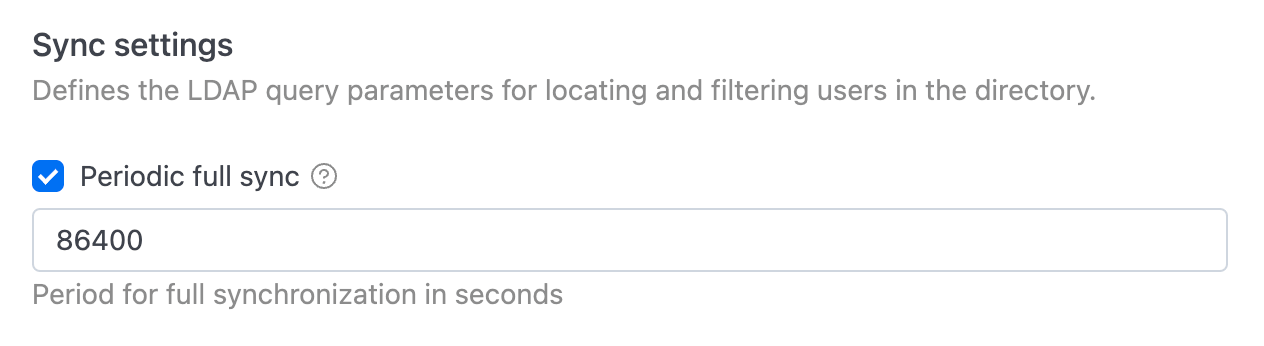
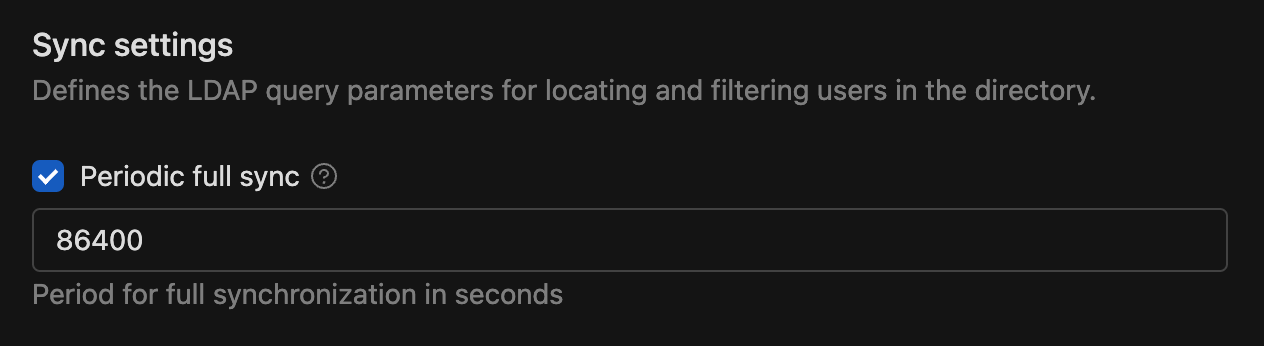
Sync Settings
Use Periodic full sync to control whether IOMETE regularly synchronizes LDAP users and groups. When enabled, enter the full sync period in seconds. The minimum is 5 seconds, and the default is 86400 seconds (24 hours).
After filling in all required information, click Save.
Validating LDAP Filters
You can validate custom user and group filters before you save the configuration.
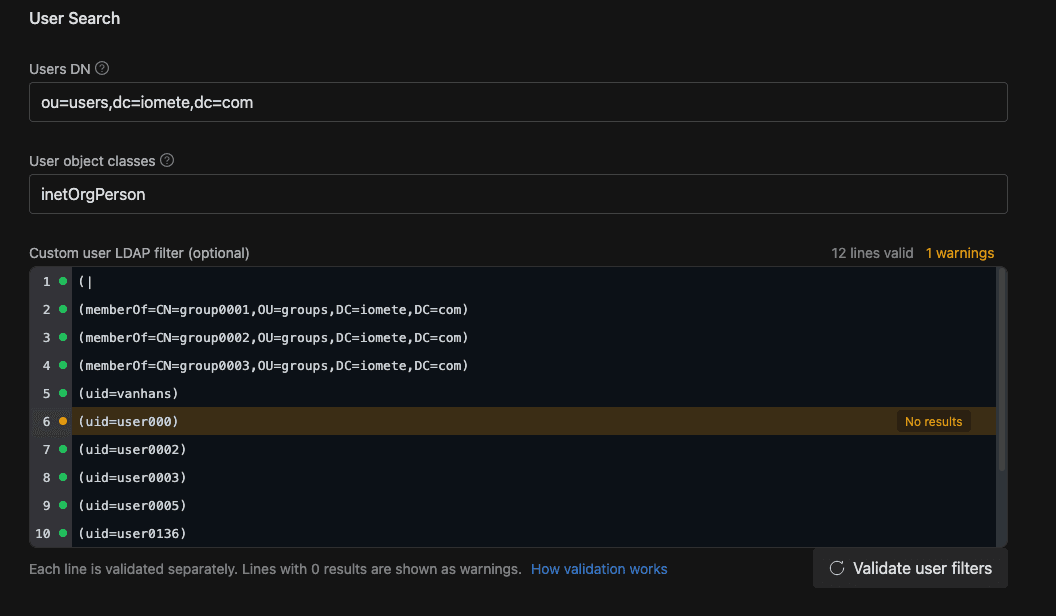
- Use Validate user filters or Validate group filters above the relevant filter editor.
- Enter one LDAP filter per line. Blank lines are ignored.
- Each validated line shows a status in the editor:
- Green means the line returned results.
- Yellow means the line returned no results.
- Red means the line produced an LDAP error.
- If the DN format is invalid, IOMETE shows an inline error on the DN field.
- If the LDAP server can't find the configured object path, IOMETE shows No such object. Check DN and object classes.
LDAP Actions
After saving the integration, you can manage LDAP from the same page.
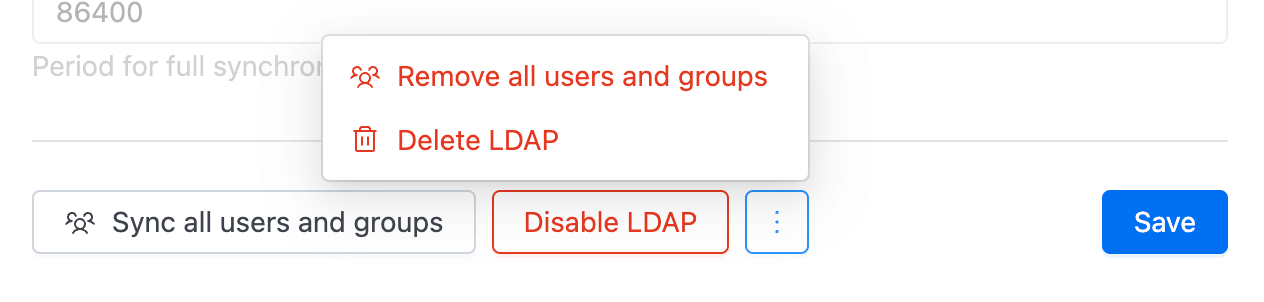
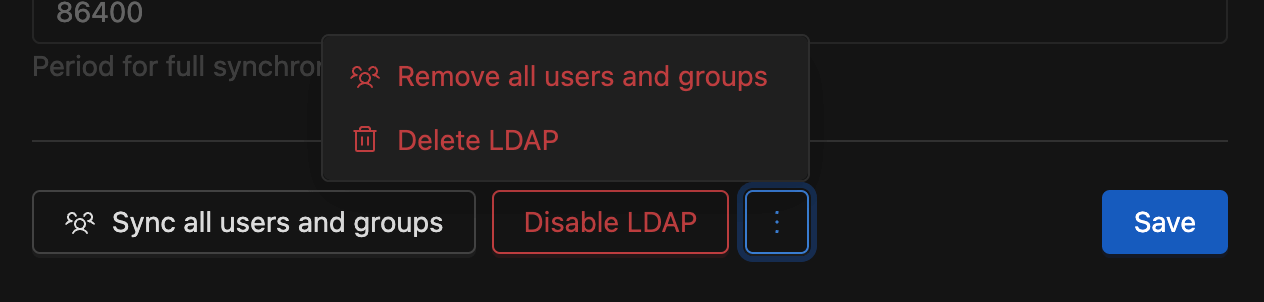
Syncing All Users and Groups
Click Sync all users or Sync all users and groups to synchronize the current LDAP users and groups with the IOMETE user and group database.
Removing Imported Users and Groups
Click Remove all users or Remove all users and groups to delete previously imported LDAP data from IOMETE without deleting the LDAP configuration itself.
Enabling or Disabling LDAP
Use Enable LDAP or Disable LDAP to turn the integration on or off. When LDAP is disabled, imported LDAP users can no longer sign in until it is enabled again.
Deleting LDAP
Click Delete LDAP to permanently remove the LDAP configuration and the LDAP users and groups imported through it.
Soft-Delete Behavior
When the identitySoftDelete feature flag is enabled, LDAP sync uses an archive-and-restore flow instead of hard-deleting imported LDAP records.
- Full sync: Existing LDAP users and groups are updated, previously archived LDAP users and groups are restored, new LDAP users and groups are created, and LDAP users and groups that no longer exist in the directory are archived. Before rebuilding the current LDAP state, IOMETE also soft-deletes LDAP user-group, user-role, group-role, and group-to-group mappings, then recreates the current mappings from the latest sync result.
- Remove all users or Remove all users and groups: IOMETE soft-deletes all LDAP-origin users, groups, and LDAP mappings, but keeps the LDAP integration settings so you can sync again later.
- Delete LDAP: IOMETE soft-deletes the LDAP integration record and soft-deletes all LDAP-origin users, groups, and LDAP mappings. After the delete completes, the page returns to create mode.
- Event logs: Full sync still writes the standard LDAP Sync audit entry. In the soft-delete path, IOMETE also writes
iam-users/USERS_SYNCEDandiam-groups/GROUPS_SYNCEDevent-log entries withcreated,updated,restored, andarchivedlists.
When the feature flag is disabled, full sync hard-cleans and re-imports LDAP data, and the remove/delete actions hard-delete imported LDAP users, groups, and mappings.
Access Permissions
All operations on the LDAP page require the IAM Manager admin role.
| Admin role | View | Create | Update | Enable/Disable | Sync | Remove imported | Delete |
|---|---|---|---|---|---|---|---|
| IAM Manager | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
| Any other role | No | No | No | No | No | No | No |
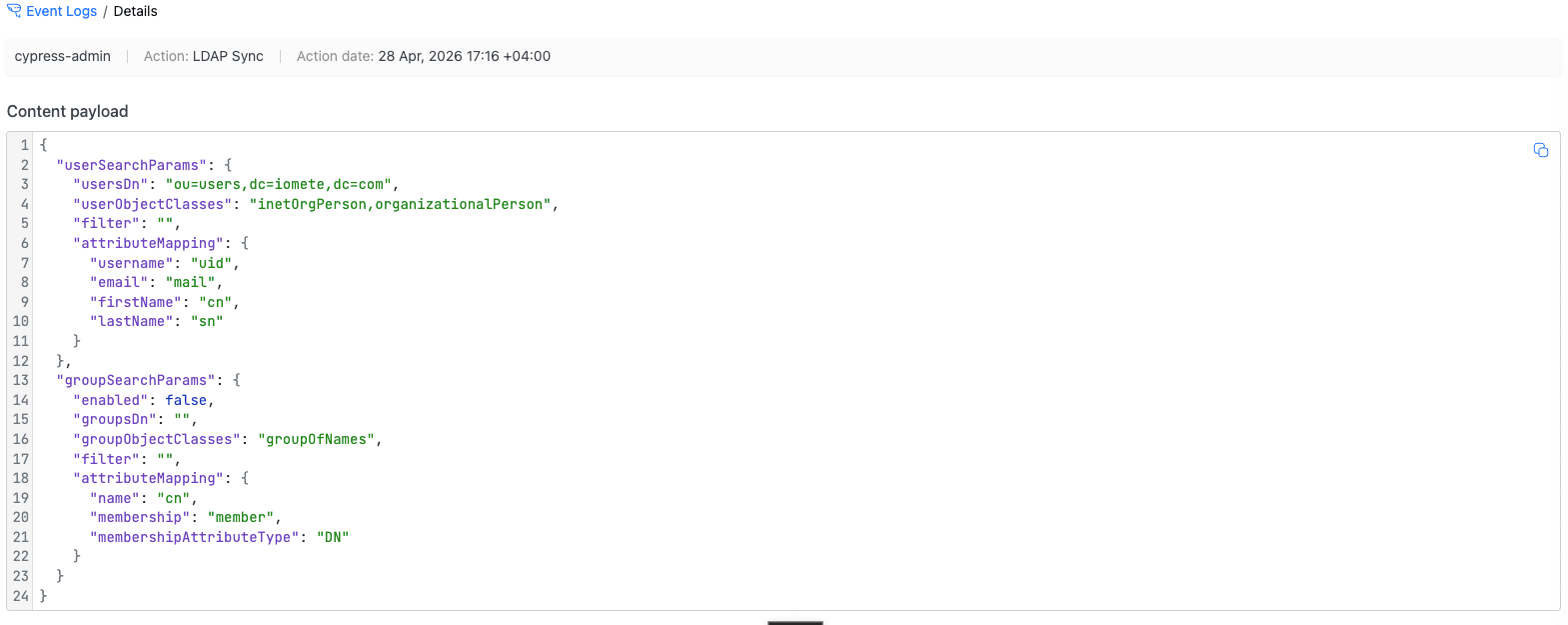
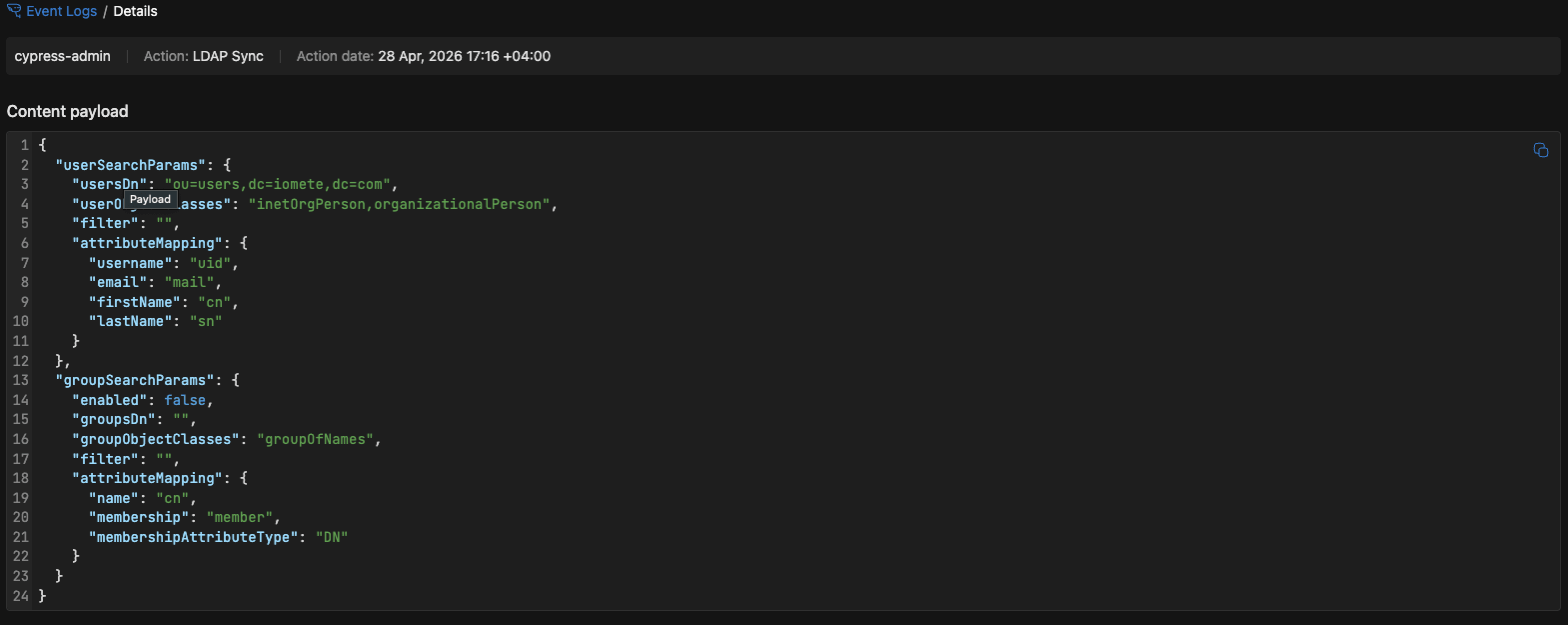
Auditing LDAP
To audit LDAP operations, go to Administration → Event Logs in Admin Portal. Here, you can view who performed LDAP-related actions and when.
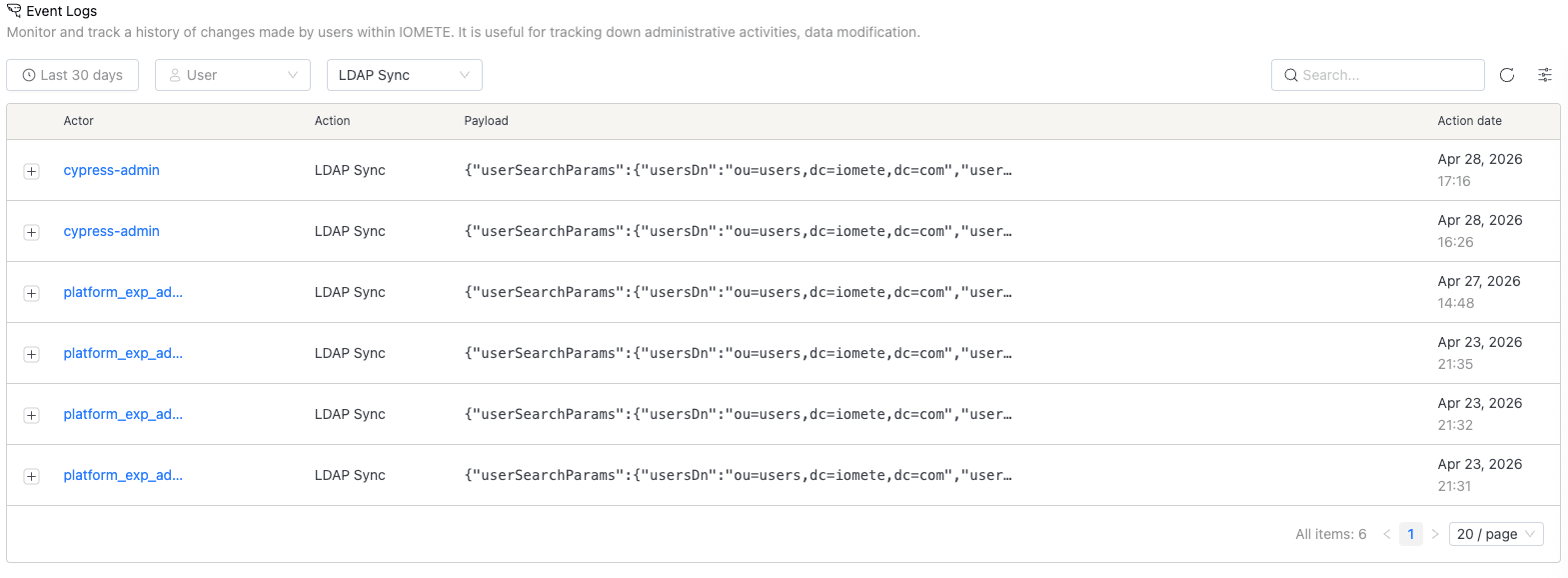
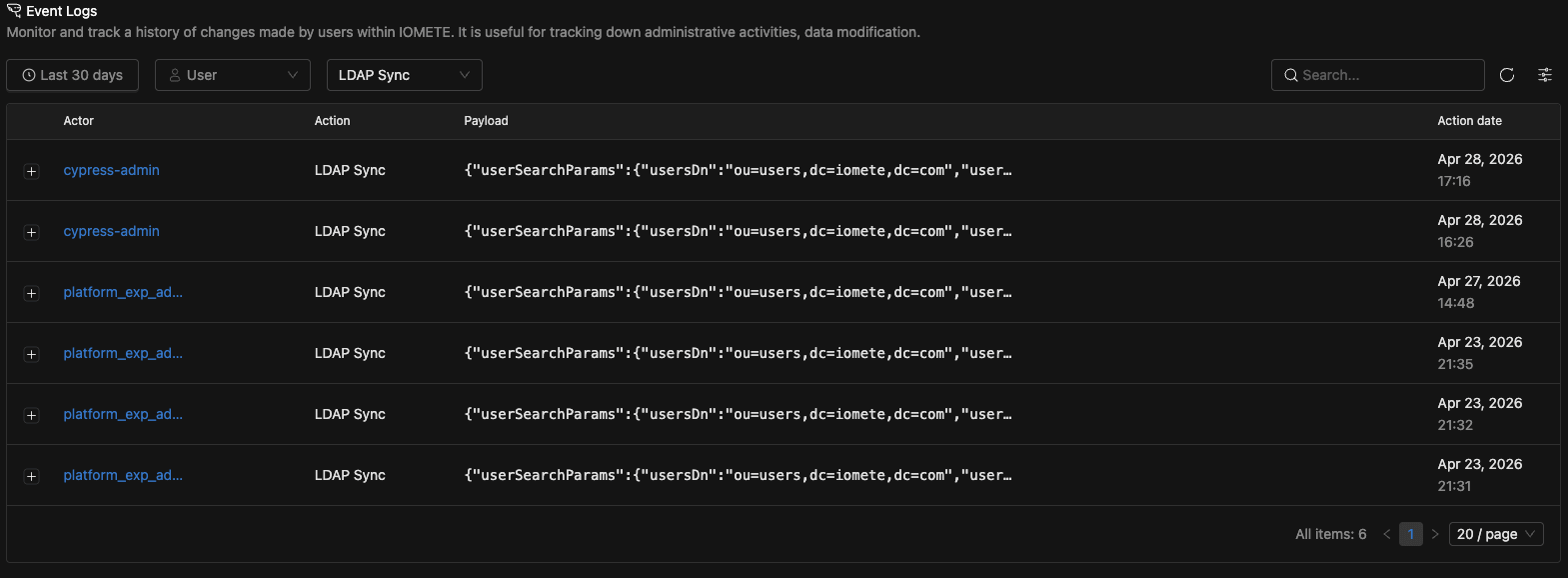
Click the + icon on the left of any entry to inspect the payload for that action.